The Information Security Office (ISO) continuously strives for daily operational excellence to ensure the confidentiality, availability, and integrity of University of Utah information technology systems and data through appropriate information security resources and best practices.
Recent News
-

Coming soon: Microsoft sensitivity labels, a new tool to help protect university data
To strengthen the protection of university information and make responsible data handling easier, UIT is preparing to roll out Microsoft 365 sensitivity labels. The new feature will help students, faculty, and staff classify and safeguard documents and emails with greater consistency and less effort.
-

IT security tip: Receive a Duo push you didn't expect?
If you received a Duo push but did not request one, you're likely the target of a multifactor authentication fatigue attack and need to take immediate action to prevent access to your university account.
-

9 U orgs celebrated for cybersecurity toolset implementation
UIT Partner Relations celebrated nine U organizations for successfully implementing a suite of cybersecurity tools. The UIT-sponsored event marked the fulfillment of a primary requirement of the campus-wide Cybersecurity Program commissioned by President Randall.
Tips & resources |
|
University-approved platforms for restricted and sensitive data
Due to the level of risk associated with restricted and sensitive data, the university has approved only a select number of platforms for those data types. Our IT security matrix provides an overview of some university and personal platforms (e.g., Adobe products, Canvas, Microsoft Copilot, and Zoom health care license) and the data types for which they are approved.

Best practices for travelers
Travel more securely whether you’re going on a roadtrip or on an international adventure. Tips include cybersecurity basics and temporary measures to better protect your information and devices while you are away from home.
A middle-aged white man (who we will call the "fisher" from now on) wearing a green fishing vest with many pockets walks through a grove of trees, holding a fishing pole and tackle box. He has short, light brown hair and scruffy facial hair, and wears a red, white, and blue flannel shirt and jeans. He sets the pole and tackle box on the ground and stretches his arms above his head. White text flies up, reading "phish•ing." More white text follows, reading:
"phish•ing /fi-SHiNG/"
"noun"
"Tricking a user into sharing personal information or login credentials by posing as an official source."
0:09: The video transitions to the fisher sitting at a desk with two computer monitors. The monitor on the left shows a document containing a pie chart; the monitor on the right shows a yacht on water. The man rubs his hands together and cracks his knuckles, then begins to type on his keyboard. Near his keyboard, under the monitors, he has Funko Pop statues and comic book figurines.
0:13: The video transitions back to the fisher in the grove of trees. The video zooms in on the fisher's hands; he holds a small, metal box containing fishing lures. He selects a lure and attaches it to his fishing line. He then walks toward a red block U statue on the University of Utah campus.
0:23: The video moves to a shared work table, where a man and woman huddle over their Apple laptops. The white man has dark, short hair and wears a light-colored button-up shirt and khaki pants; the white woman has long, dark, wavy hair and wears a black dress. She holds a dark folder open in her lap. A woman sits adjacent to them, wearing headphones and using her Apple laptop. She has dark hair pulled into a bun and wears dark glasses and a light-colored hoodie.
0:25: The video transitions back to the fisher, who stands in front of the "Imagine U" side of Marriott Library, casting his fishing line toward the building. He walks through campus again, passing a set of stairs and multiple street lamps. He then casts his line toward a white female student passing by on the sidewalk, which is lined with trees full of leaves. The red block U is behind him on the left. The student — who is wearing a multicolored, short-sleeved shirt with chevron patterns, black pants, and a backpack — shies away.
0:35: The fisher continues casting his line in various places around campus. In one scene, he even pops out beyond a bush to startle a man passing by. The white man is wearing a blue button-down shirt with the sleeves rolled up and jeans. In another scene, the fisher casts his line toward a white male man who is walking his bike on the sidewalk. The cyclist has long light brown or blond hair, and wears red flannel, dark jeans, a red and white hat, and a backpack and carries a light-colored helmet. He ducks from the fishing line.
0:41: In the next scene, the fisher climbs a rock and looks out over the landscape. He then appears to reel in his fishing line, which is taut. Text fades in from the left, reading "You will never receive a threatening or intimidating email from any legitimate University source."
0:48: The video transitions to a man, whose face we cannot see, typing on a black laptop with a U drum and feather sticker and a white sticker in the shape of Alaska. He is wearing a white shirt with a dark graphic, Apple headphones, and a red and white braided bracelet. On the desk, there is a couple of notebooks, and red and blue pens. Light filters in behind him. Text fades in from the left, reading "Never share your uNID and password with anyone."
0:53: The video transitions to a black screen that shows icons and text on the common signs of phishing scams, including the "no" symbol and a tip that reads: "Common Phishing Scams." A pointer moves to reveal the following bullet points:
- "Unusual email language, poor spelling or grammar"
- "The URL doesn't match webpage"
1:02: The video then moves to into an example of a webpage in the Safari browser. The URL reads "www.TAKEALLYOURMONEYANDRUN.org," and the page imitates a University of Utah login screen. A browser tab in the background reads, "Funny Cats — YouTube." The video zooms in on the URL, which is highlighted with a white overlay while the rest of the screen is darkened by a black overlay.
1:05: The video returns to the bullet point list of common phishing scams. The next item reads, "When hovering over link, it doesn't match the promised content."
1:08: The screen transitions to an email client, which shows an example of an email. Highlighted is a link that reads, "here" but shows a URL to "http://takeallyourmoneyandrun.org."
1:11: The video transitions into a library, where an Asian man sits at a desk with his hands on the keyboard of the laptop open in front of him. He is wearing a checkered button-down shirt with the sleeves pushed up and a pair of glasses. His hair is black and a bit long around the ears, forehead, and back of the neck. A backpack or messenger bag is on the table next to his laptop, and a chair is open to his left. In the background, light filters in from large windows and two stacks/shelves hold numerous books.
1:15: The video zooms in on the Asian man and his laptop. On the screen, text reads "Guard your uNID and password like your Social Security number." Then video transitions into a montage of shots of people using open laptops. The first image shows a desk with an open laptop, which has multiple windows open. White hands barely touch the edge of the keyboard. Text fades in that reads "Change your password often." The second image shows a white man using the touch pad on his laptop to scroll. We only see his hands and the sleeves of his button-down shirt, which is white checkered with dark lines. The third image shows a white woman using a silver laptop. She faces us so we cannot see what is on the screen. She has long, brown hair and wears a dark T-shirt. To her right, another white person, who appears to be a woman, types on a laptop. This person is wearing a gray sweatshirt or hoodie. Text fades in that reads "Change your password and call the Campus Help Desk immediately." A phone number reading "801-581-4000" fades in.
1:25: The video transitions back to an outdoor space on campus with grass and trees. A man in a light blue-green shirt and dark pants walks left past our view. Another man, somewhat balding, walks right past our view. He wears a dark blue or black shirt with short sleeves and a collar, and jeans. The fisher is in the background, waving his fishing line.
1:29: The video returns to the fisher's desk, with a close-up on the Funko pop and comic book figurines. The figurines include Superman and a shark, but it's not clear which characters the others represent. The video zooms out so we can see the fisher sitting at the desk. He makes a fist with his right hand and pulls it downward in a motion that represents cha-ching, yes, score, gotcha, or a similar celebration. He throws his head back and laughs.
1:32: The screen goes black. The University Information Technology (UIT) logo (white text with a red Block U) and white text reading "it.utah.edu/" fade in, with the word "security" added shortly after to the end of the URL so it reads "it.utah.edu/security."
1:37: The screen changes to a white background with a gray gradient at the bottom that shows a mirror image of the red and black Imagine U logo in the center of the screen.
Phishing is becoming more and more popular.
We're talking about phishing with a "ph." Not the river-runs-through-it kind.
It's about cyber scammers, con artists, and thieves. Every day they're baiting and hooking personal information and gutting bank accounts. It's happening all around the nation and right here at the U.
Faculty, staff, and students are all vulnerable, and attacks are becoming more targeted.
Because some university personal information is readily available, scammers are often using it, along with emotional responses, to get you to act.
It's important to stay vigilant and know thieves are trying to land the big one.
You will never receive a threatening or intimidating email from any legitimate university source.
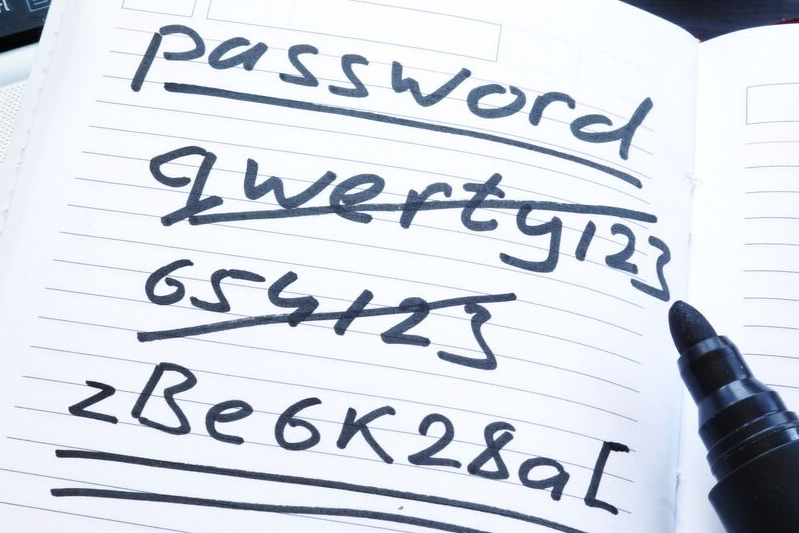
Don't take the bait. Never share your uNID and password with anyone. And look for the signs that are common in phishing scams. Things like:
- unusual email language or spelling or grammar
- the URL doesn't match the webpage
- when hovering over a link, it doesn't match the promised content
Here's what to do to stay protected:
- Guard your uNID and password like your Social Security number
- Change your passwords often
- Lock your screens when not in use or when you leave your desk
If you've been hooked, call the Campus Help Desk (801-581-4000, option 1) immediately.
Trust your gut. If it smells fishy, it probably is.
For more information, visit it.utah.edu.
Phishing lessons
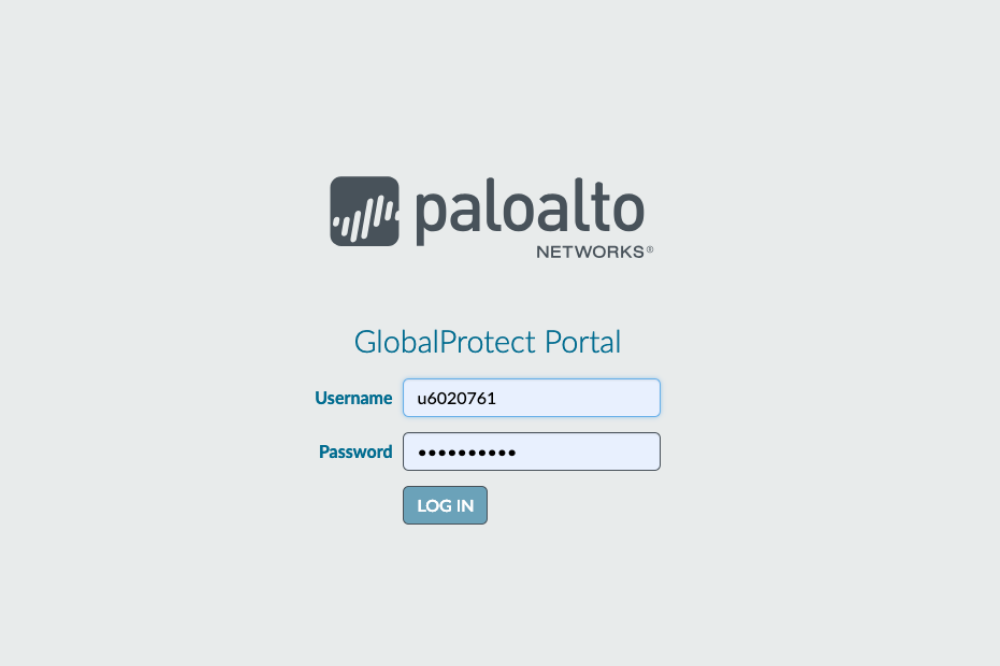
You realize it a moment too late: You fell for a malicious email, opened a bad link, and entered your password on a suspicious site. You’ve just been phished! Now what?
If you open a questionable link and enter login credentials, immediately change your password in the CIS portal — and in any personal accounts that may be compromised. In addition, contact the ISO’s Security Operations Center at soc@utah.edu to notify information security staff.
Whenever you receive a phishing attempt through a university email account, report it. Use the Phish Alert button or forward the email as an attachment to phish@utah.edu.